Category: Firewall
Are you ready to change your security paradigm?
Most application stacks built today rely on decades-old security paradigm: individual components of the stack (web servers, app servers, database servers, authentication servers ...) are placed in different security zones implemented with separate physical devices, VLANs or some other virtual networking mechanism of your choice.
The security zones are then connected with one or more firewalls (when I was young we used routers with packet filters), resulting in a crunchy edge with squishy core architecture.
The Impact of Changed NHRP Behavior in DMVPN Networks
Two years ago I wrote the another Fermatish post: I described how NHRP behavior changed in DMVPN networks using NAT and claimed that it might be a huge problem, without ever explaining what the problem is.
Fabrice quickly identified the problem, but it seems the description was not explicit enough as I’m still getting queries about that post, so here’s a step-by-step description of what’s going on.
The Spectrum of Firewall Statefulness
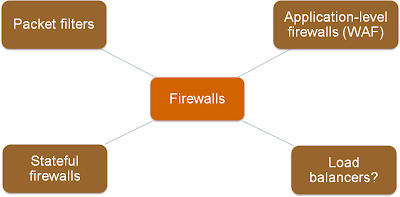
One of the first slides I created for the Virtual Firewalls webinar explained various categories of traffic filters, from stateless (and fast) packet filters to application-level firewalls.
As always, the real life is not black-and-white; I found a whole spectrum of products in the wild.
IPv6 addressing in SMB environment
Martin Bernier has decided to open another can of IPv6 worms: how do you address multiple subnets in a very typical setup where you use a firewall (example: ASA) to connect a SMB network to the outside world?
Redundant Data Center Internet Connectivity – Problem Overview
During one of my ExpertExpress consulting engagements I encountered an interesting challenge:
We have a network with two data centers (connected with a DCI link). How could we ensure the applications in a data center stay reachable even if all local Internet links fail?
On the face of it, the problem seems trivial; after all, you already have the DCI link in place, so what’s the big deal ... but we quickly figured out the problem is trickier than it seems.
What Exactly Are Virtual Firewalls?
Kaage added a great comment to my Virtual Firewall Taxonomy post:
And many of physical firewalls can be virtualized. One physical firewall can have multiple virtual firewalls inside. They all have their own routing table, rule base and management interface.
He’s absolutely right, but there’s a huge difference between security contexts (to use the ASA terminology) and firewalls running in VMs.
Virtual Firewall Taxonomy
Based on readers’ comments and recent discussions with fellow packet pushers, it seems the marketing departments and industry press managed to thoroughly muddy the virtualized security waters. Trying to fix that, here’s my attempt at virtual firewall taxonomy.
Firewalls in a Small Private Cloud
Mrs. Y, the network security princess, sent me an interesting design challenge:
We’re building a private cloud and I'm pushing for keeping east/west traffic inside the cloud. What are your opinions on the pros/cons of keeping east/west traffic in the cloud vs. letting it exit for security/routing?
Short answer: it depends.
Why is OpenFlow focused on L2-4?
Another great question I got from David Le Goff:
So far, SDN is relying or stressing mainly the L2-L3 network programmability (switches and routers). Why are most of the people not mentioning L4-L7 network services such as firewalls or ADCs. Why would those elements not have to be SDNed with an OpenFlow support for instance?
To understand the focus on L2/L3 switching, let’s go back a year and a half to the laws-of-physics-changing big bang event.
Is NAT a Security Feature?
15 years after NAT was invented, I’m still getting questions along the lines of “is NAT a security feature?” Short answer: NO!
Longer answer: NAT has some side effects that resemble security mechanisms commonly used at the network edge. That does NOT make it a security feature, more so as there are so many variants of NAT.