Category: Security
IPv6 Source Address Validation Improvement
We learned how to deal with ARP and IP spoofing in IPv4 networks. Every decent switch has DHCP snooping, ARP protection, and IP source guard (or whatever the features are called), but validating source IPv6 addresses in security-conscious environments or public multi-access networks remains a major headache.
It would be pretty easy to solve the problem with a central controller, but IETF decided to go another way and developed yet another framework: Source Address Validation Improvements (SAVI). For more information, watch the following video from IPv6 Security webinar in which Eric Vyncke describes the intricacies of SAVI in great details.
The Spectrum of Firewall Statefulness
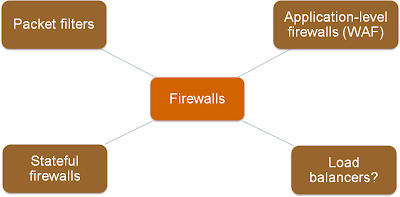
One of the first slides I created for the Virtual Firewalls webinar explained various categories of traffic filters, from stateless (and fast) packet filters to application-level firewalls.
As always, the real life is not black-and-white; I found a whole spectrum of products in the wild.
IPv6 Secure Neighbor Discovery (SEND)
During the IPv6 Security webinar, Eric Vyncke explained the intricate details of IPv6 Security Neighbor Discovery (SEND) and the reasons it will probably never take off.
BGP Security draft adopted as IETF workgroup document
We published the first draft of the BGP Operations and Security document almost a year ago. In the meantime, the authors and Merike Kaeo presented the draft at RIPE and IETF meetings and collected literally tons of feedback (well documented in change logs) ... and finally the draft was adopted as IETF opsec workgroup document and republished under a new name.
We would never get this far without relentless Jerome Durand who did most of the editing heavy lifting, persistent nudging from Gunter Van de Velde and gracious help of Merike Kaeo. Thank you all!
Extending MPLS/VPN to Customer Sites
Erich has encountered a familiar MPLS/VPN design challenge:
We have Cisco's 2901s with the data license running MPLS/VPN on customer site (the classical PE is at the customer site). Should we use eBGP between CPE router and network edge router, some sort of iBGP route reflector design, or something completely different?
The “it depends” answer depends primarily on how much you can trust the routers installed at the customer site (CPE routers).
Reconnaissance in IPv6
In the introductory part of the IPv6 security webinar, Eric Vyncke explained how the huge IPv6 subnet sizes won’t stop a determined attacker, but will make the task of network or security engineers trying to take host inventory much harder.
IPv6 Router Advertisements Deep Dive
I’m constantly getting questions about the intricate interworking of various flags present in IPv6 Router Advertisement messages. Here’s a (hopefully comprehensive) summary taken primarily from RFC 4861.
IPv6 deployment IETF drafts
An incredible amount of IPv6 deployment documents has been published as IETF drafts recently, amongst them:
- Operational security considerations for IPv6 networks
- Design guidelines for IPv6 networks
- Stateless IP/ICMP Translation in IPv6 Data Centre Environments (aka IPv6-only data centers)
- Enterprise IPv6 Deployment Guidelines
Enjoy ... and don’t forget to join the v6ops mailing list ;)
What Exactly Are Virtual Firewalls?
Kaage added a great comment to my Virtual Firewall Taxonomy post:
And many of physical firewalls can be virtualized. One physical firewall can have multiple virtual firewalls inside. They all have their own routing table, rule base and management interface.
He’s absolutely right, but there’s a huge difference between security contexts (to use the ASA terminology) and firewalls running in VMs.
Virtual Firewall Taxonomy
Based on readers’ comments and recent discussions with fellow packet pushers, it seems the marketing departments and industry press managed to thoroughly muddy the virtualized security waters. Trying to fix that, here’s my attempt at virtual firewall taxonomy.