Configuration Change Logging ignores the configuration downloads
The Configuration Change Notification and Logging feature is supposed to log changes to the router's configuration. While it does a great job of logging commands entered in the router configuration mode, it completely ignores configuration changes due to configuration download (for example, with configure network or copy tftp running-config command).
Which switching path does an IOS feature use
I've got an excellent question recently: Which switching path is used in Zone-based firewalls when a packet is dropped? As usual, IOS documentation was not very helpful (which is understandable as the answer might depend on hardware platform, interface encapsulation, other features configured on the router etc.). However, there is a great tool to use - the show interface stats command.
Fine-Tuning CEF Load Balancing
In environments with a low number of IP hosts you have to fine-tune the CEF load-sharing algorithm to ensure that the traffic is spread between all parallel paths. A typical scenario is a primary-backup data center setup with pairs of replicating servers, as shown in the figure below.
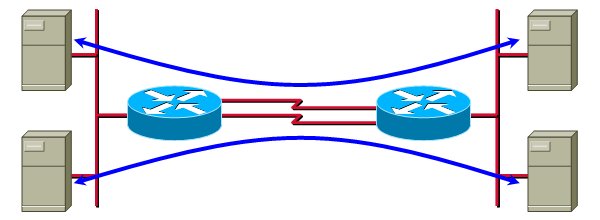
In these cases, you have to try different values of seed parameter of the CEF universal algorithm.
Local username authentication
As I get a lot of hits from Google refering to local login, here's the whole story: Cisco IOS supports local username/password based authentication (almost) forever (it's been there even before the AAA architecture). To change from simple password-based authentication to username+password based on, use login local configuration command on console and/or VTY lines. The local usernames and passwords are defined with the username configuration command.
IOS HTTP client sets Host: field to IP address
Update 2012-08-27: Stefan de Kooter reported the bug had been fixed in IOS release 15.1(4)M.
If you run multiple web sites on a single physical server, it's highly likely that you rely on the ability of HTTP/1.1 clients to specify the Host: field in the HTTP request to indicate which web site they're trying to access.
Cisco IOS always inserts the web server's IP address (not the hostname) in the Host: field of the HTTP request, regardless of whether you enter IP address or hostname in the URL part of an IOS command that supports HTTP (for example, copy or more command) ... and regardless of whether the hostname is locally configured with the ip host command or resolved by an external DNS server specified in the ip name-server command.
Log terminal access to your router
In a previous post, I've shown how you can log the changes in interactive user's privilege level. With the Cisco IOS Login Enhancements (introduced in IOS release 12.3(4)T, integrated in 12.4), you can also log all login successes and failures, even when using local user database (a similar functionality was previously achievable only when using central TACACS+ or RADIUS server).
The configuration commands to enable terminal access logging are login on-success log and login on-failure log. You can also specify that you want send SNMP traps in these circumstances (with the trap option) or that you only want to log every Nth attempt with the every n option.
Log user privilege level changes
The logging userinfo configuration command introduced in IOS release 12.3T (integrated into 12.4) starts logging of all changes in user privilege levels (as requested by enable or disable commands).
Network Statements in the OSPF Process Are No Longer Order-Dependent
When I was still teaching Cisco courses, we were telling the students that the order of network statements in an OSPF process was important if their ranges were overlapping; the first network statement that matched an interface IP address would place that interface in the corresponding area. This is no longer true; Cisco IOS now properly handles overlapping network area configuration commands.
Consider the following example:
Deploying Zone-Based Firewalls
Cisco Press has just released my latest book (and my first digital one): Deploying Zone-Based Firewalls. The book covers a completely new way to configure IOS firewall feature set based on security zones you define on a router and inter-zone policies configured using the familiar class-maps and policy-maps.
You can preview this digital book (they call it Digital Short Cut) using the Safari technology at Cisco Press and buy it at Amazon.
Reduce the noise generated by the Cisco IOS copy command
I always hate it when Cisco IOS asks me for things I've already supplied in a command line, the most notable case being the copy command. For example, if you supply the complete source and destination file name in the command line, IOS still insists on asking you all the same questions (at least filling in the parameters I've supplied in the command line):
